A new cyberattack method called Grokking is exploiting X’s AI assistant, Grok, to distribute malware through malicious links. Researchers at Guardio Labs revealed the technique on September 4.
The attack hides malicious URLs in the “From:” metadata of promoted video-card posts. Ads often use sensational or adult content to attract attention while concealing the malware. Attackers reply to their own posts, tagging Grok with questions like “Where is this video from?” Grok, trusted as a system account, reads the hidden metadata and exposes the malicious link in its public response. Paid ad amplification further increases exposure, generating hundreds of thousands to millions of impressions.
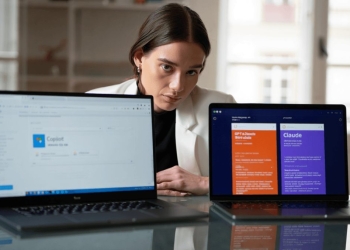
Grokking is part of a growing trend where criminals repurpose mainstream AI models such as Grok and Mistral’s Mixtral. These threat actors wrap models in jailbroken interfaces to bypass safety filters, creating tools that can generate phishing emails, malware code, and tutorials for novice hackers. According to Cato Networks, access to these illicit AI tools costs only a few hundred euros. Past examples include an “Uncensored Assistant” powered by Grok and a Mixtral-based variant.
The primary risk comes not from the AI models themselves but from how attackers exploit system prompts and trusted accounts. Grokking shows that even widely trusted AI tools can be weaponized when combined with social engineering and platform vulnerabilities. Security experts warn that millions of users may have been exposed to malicious websites, emphasizing the urgent need for better safeguards and awareness of AI-enabled threats.
Users should be cautious when clicking links, even if they appear verified or AI-generated. Platforms like X need stricter metadata vetting and better controls to prevent AI-assisted malware delivery. Recognizing that trusted AI systems can be exploited is essential for protecting both individual users and organizational networks from emerging AI-driven cybercrime.